
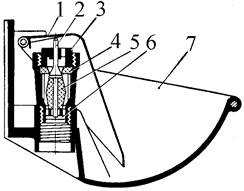
Индивидуальные и групповые автопоилки: для животных. Схемы и конструкции...
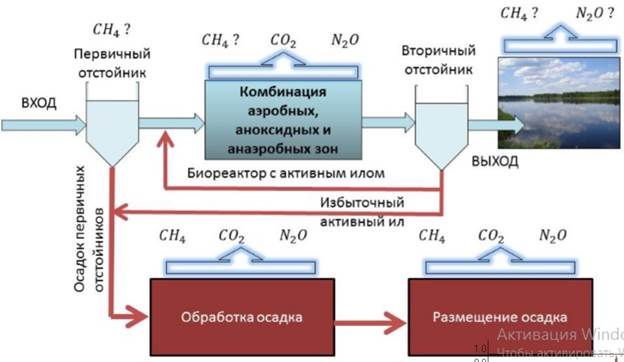
Эмиссия газов от очистных сооружений канализации: В последние годы внимание мирового сообщества сосредоточено на экологических проблемах...
Индивидуальные и групповые автопоилки: для животных. Схемы и конструкции...
Эмиссия газов от очистных сооружений канализации: В последние годы внимание мирового сообщества сосредоточено на экологических проблемах...
Топ:
Теоретическая значимость работы: Описание теоретической значимости (ценности) результатов исследования должно присутствовать во введении...
Когда производится ограждение поезда, остановившегося на перегоне: Во всех случаях немедленно должно быть ограждено место препятствия для движения поездов на смежном пути двухпутного...
Определение места расположения распределительного центра: Фирма реализует продукцию на рынках сбыта и имеет постоянных поставщиков в разных регионах. Увеличение объема продаж...
Интересное:
Отражение на счетах бухгалтерского учета процесса приобретения: Процесс заготовления представляет систему экономических событий, включающих приобретение организацией у поставщиков сырья...
Подходы к решению темы фильма: Существует три основных типа исторического фильма, имеющих между собой много общего...
Инженерная защита территорий, зданий и сооружений от опасных геологических процессов: Изучение оползневых явлений, оценка устойчивости склонов и проектирование противооползневых сооружений — актуальнейшие задачи, стоящие перед отечественными...
Дисциплины:
|
из
5.00
|
Заказать работу |
“History of information security”
Since the early days of communication, diplomats and military commanders understood that it was necessary to provide some mechanism to protect the confidentiality of correspondence and to have some means of detecting tampering. Julius Caesar is credited with the invention of the Caesar cipher c. 50 B.C., which was created in order to prevent his secret messages from being read should a message fall into the wrong hands, but for the most part protection was achieved through the application of procedural handling controls. Sensitive information was marked up to indicate that it should be protected and transported by trusted persons, guarded and stored in a secure environment or strong box. As postal services expanded, governments created official organizations to intercept, decipher, read and reseal letters (e.g. the UK Secret Office and Deciphering Branch in 1653).
In the mid-19th century more complex classification systems were developed to allow governments to manage their information according to the degree of sensitivity. The British Government codified this, to some extent, with the publication of the Official Secrets Act in 1889. By the time of the First World War, multi-tier classification systems were used to communicate information to and from various fronts, which encouraged greater use of code making and breaking sections in diplomatic and military headquarters. In the United Kingdom this led to the creation of the Government Code and Cypher School in 1919.
Encoding became more sophisticated between the wars as machines were employed to scramble and unscramble information. The volume of information shared by the Allied countries during the Second World War necessitated formal alignment of classification systems and procedural controls. An arcane range of markings evolved to indicate who could handle documents (usually officers rather than men) and where they should be stored as increasingly complex safes and storage facilities were developed. Procedures evolved to ensure documents were destroyed properly and it was the failure to follow these procedures which led to some of the greatest intelligence coups of the war.
The end of the 20th century and early years of the 21st century saw rapid advancements in telecommunications, computing hardware and software, and data encryption. The availability of smaller, more powerful and less expensive computing equipment made electronic data processing within the reach of small business and the home user. These computers quickly became interconnected through the Internet.
The rapid growth and widespread use of electronic data processing and electronic business conducted through the Internet, along with numerous occurrences of international terrorism, fueled the need for better methods of protecting the computers and the information they store, process and transmit. The academic disciplines of computer security and information assurance emerged along with numerous professional organizations – all sharing the common goals of ensuring the security and reliability of information systems.
Ex.10. Make a presentation on one of the following topics.
1. Information security in ancient Rome.
2. Information security in Middle Ages.
3. Information security in modern world.
4. Information security in business and industry.
5. Information security in personal privacy
Presentation requirements: format – MS Power Point, number of slides from 10 to 15, animation (optional, but recommended), presentation plan - from 5 to 10 points, performance time - from 5 to 7 minutes.
UNIT 2
Ex.1. Read and translate the text.
Risk management
Risk management is the process of identifying vulnerabilities1 and threats to the information resources used by an organization in achieving business objectives, and deciding what countermeasures, if any, to take in reducing risk to an acceptable level, based on the value of the information resource to the organization.
There are two things in this definition that may need some clarification. First, the process of risk management is an ongoing iterative2 process. It must be repeated indefinitely. The business environment is constantly changing and new threats and vulnerability emerge every day. Second, the choice of countermeasures (controls) used to manage risks must strike a balance between productivity, cost, effectiveness of the countermeasure, and the value of the informational asset being protected.
Risk is the likelihood that something bad will happen that causes harm to an informational asset (or the loss of the asset). Vulnerability is a weakness that could be used to endanger or cause harm to an informational asset. A threat is anything (man-made or act of nature) that has the potential to cause harm. The likelihood that a threat will use a vulnerability to cause harm creates a risk. When a threat does use a vulnerability to inflict harm, it has an impact. In the context of information security, the impact is a loss of availability, integrity, and confidentiality, and possibly other losses (lost income, loss of life, loss of real property).
Risk assessment3 is carried out by a team of people who have knowledge of specific areas of the business. Membership of the team may vary over time as different parts of the business are assessed. The assessment may use a subjective qualitative analysis based on informed opinion, or where reliable dollar figures and historical information is available, the analysis may use quantitative analysis. The research has shown that the most vulnerable point in most information systems is the human user and operator.
In broad terms, the risk management process consists of number of processes that include identification of assets and estimation of their value, conduction of a threat assessment4, vulnerability assessment and procedures required to control them. It’s necessary to evaluate the effectiveness of the control measures without discernible loss5 of productivity.
For any given risk, Executive Management can choose to accept the risk upon the relative low value of the asset, the relative low frequency of occurrence, and the relative low impact on the business. Or, leadership may choose to mitigate therisk6 by selecting and implementing appropriate control measures to reduce the risk. In some cases, the risk can be transferred to another business by buying insurance or outsourcing7 to another business.
When Management chooses to mitigate a risk, they will do so by implementing one or more of three different types of controls.
Administrative.
Administrative controls (also called procedural controls) consist of approved written policies, procedures, standards and guidelines. They inform people on how the business is to be run and how day to day operations are to be conducted. Laws and regulations created by government bodies are also a type of administrative control. The examples of administrative controls include the corporate security policy, password policy, hiring policies8 etc. Administrative controls form the basis for the selection and implementation of logical and physical controls. Administrative controls are of paramount importance.
Logical.
Logical controls (also called technical controls) use software and datato monitor and control access to information and computing systems. For example: passwords, network and host9 based firewalls10, network intrusion detection systems, access control lists, and data encryption are logical controls. A frequently overlooked11 logical control is the principle of least privilege12. This principle requires that an individual, program or system process is not granted any more access privileges than are necessary to perform the task. An example of this principle failure can occur if an individual collects additional access privileges over time. This happens when employees have their job duties13 changed, or they are promoted, or they transfer to another department. The access privileges required by their new duties are frequently added onto their already existing access privileges which may no longer be necessary or appropriate.
Physical.
Physical controls monitor and control the environment of the workplace and computing facilities. They also monitor and control access to and from such facilities. For example: doors, locks, heating and air conditioning, smoke and fire alarms, fire suppression systems14, cameras, barricades, fencing15, security guards, cable locks, etc. A frequently overlooked physical control is the separation of duties. Separation of duties ensures that an individual cannot complete a critical task by himself. For example: an employee who submits a request for reimbursement16 should not also be able to authorize payment or print the check.
NOTES
1. vulnerability (security vulnerability) – уязвимость, слабое место
2. iterative – итеративный, повторяющийся.
3. risk assessment – оценка рисков (определение возможных потерь из –за недостатка информации или её утраты при восстановлении системы).
4. threat assessment – оценка угроз
5. discernible loss – ощутимая потеря
6. to mitigate the risk – снижать риск
7. outsourcing – привлечение соисполнителей, аутсорсинг
8. hiring policies – политика найма
9. host – главный компьютер
10. firewall – межсетевой экран (МЭ), брандмауэр, защитная система, сетевой заслон
11. least privilege – минимум полномочий
12. employees' job duties – обязанности сотрудников
13. fire suppression system–система пожаротушения
14. fencing – ограждение, установка ограждений
15. overlook игнорировать, недооценивать, пренебрегать
16. reimbursement – возмещение, компенсация

Типы оградительных сооружений в морском порту: По расположению оградительных сооружений в плане различают волноломы, обе оконечности...
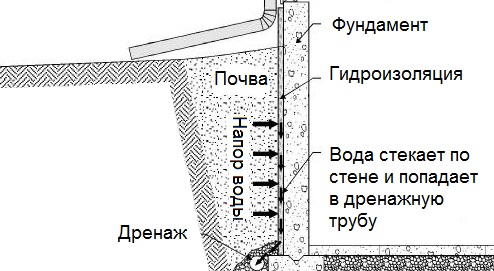
Общие условия выбора системы дренажа: Система дренажа выбирается в зависимости от характера защищаемого...
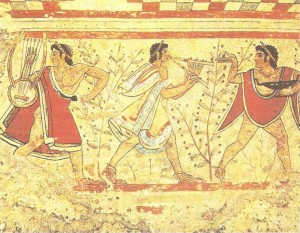
Археология об основании Рима: Новые раскопки проясняют и такой острый дискуссионный вопрос, как дата самого возникновения Рима...
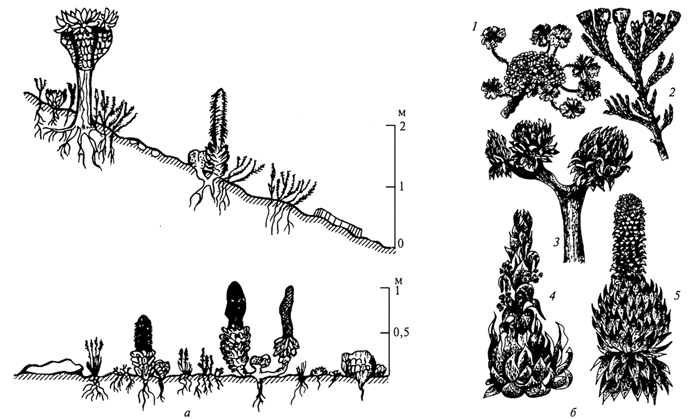
Адаптации растений и животных к жизни в горах: Большое значение для жизни организмов в горах имеют степень расчленения, крутизна и экспозиционные различия склонов...
© cyberpedia.su 2017-2024 - Не является автором материалов. Исключительное право сохранено за автором текста.
Если вы не хотите, чтобы данный материал был у нас на сайте, перейдите по ссылке: Нарушение авторских прав. Мы поможем в написании вашей работы!